HackerOne Net Worth is a pioneering platform in the bug bounty world, revolutionizing the way organizations address cybersecurity vulnerabilities. Founded in 2011 by Cody Cornell, HackerOne started as a humble startup, navigating the early challenges of facilitating bug submissions. With Cornell at the helm as CEO, the company’s vision at inception was to democratize cybersecurity by empowering hackers to work with organizations to identify and fix vulnerabilities.
In this narrative, we’ll delve into the fascinating world of HackerOne, exploring its revenue streams, growth strategies, impact on cyber security, key players, expansion into new markets, and the role it plays in digital transformation and the bug bounty industry.
HackerOne’s bug bounty model has transformed the security landscape by offering incentives to hackers for identifying vulnerabilities in organizations’ digital products. This model has led to proactive vulnerability identification and disclosure, significantly improving cybersecurity. With its robust platform and advisory board comprising industry experts, HackerOne has cemented its position as a market leader in the bug bounty space.
HackerOne’s Foundational Role in the Bug Bounty World

In 2011, a small startup named HackerOne emerged as a pioneering force in the bug bounty world, revolutionizing the way companies approached bug submissions and rewards. At the time, bug bounty programs were a relatively new concept, and most companies were still hesitant to open their doors to external penetration testing. HackerOne’s innovative approach would change all that.Founded by Morgan Sjogren and Sui Jiuyi, HackerOne began as a platform designed to facilitate bug submissions and connect companies with the world’s top security researchers.
The early days were marked by challenges, as the company navigated the complexities of building a robust yet user-friendly platform. However, with dedication and perseverance, HackerOne’s vision began to take shape.
Chief Executive Officer Cody Cornell: Early Leadership and Vision, Hackerone net worth
Enter Cody Cornell, one of the company’s early leaders and current Chief Executive Officer. Under Cornell’s guidance, HackerOne’s vision for a collaborative and transparent bug bounty world began to take hold. Cornell’s leadership played a crucial role in shaping HackerOne’s early growth and direction.Cornell’s vision for HackerOne was centered around empowerment – empowering researchers to find and report bugs, and empowering companies to harness the collective expertise of the global security community.
He recognized that the traditional bug bounty model, where companies paid researchers for individual discoveries, was limited in its potential. HackerOne’s platform aimed to break down silos and foster a culture of collaboration, where researchers could pool their knowledge and share insights to collectively improve cybersecurity.
Early Challenges and Innovations
As HackerOne began to gain traction, the company faced several challenges, including:
- Scalability: With the rapid growth of user contributions and bug submissions, HackerOne needed to develop scalable architecture to manage the influx of data.
- Security: Ensuring the security and integrity of submitted bugs and user data was paramount, as hackers could potentially exploit vulnerabilities for malicious purposes.
- Community building: Fostering a community of researchers and companies required creating a platform that encouraged collaboration and open communication.
To address these challenges, HackerOne innovated its platform to incorporate machine learning algorithms, which enabled the automation of bug categorization, prioritization, and validation. This not only streamlined the bug triage process but also allowed researchers to focus on high-priority issues. Additionally, HackerOne developed a robust community forum, where users could discuss security topics, share knowledge, and participate in collaborative bug hunting exercises.
Visionary Approach and Collaboration
Cornell’s leadership and vision played a pivotal role in HackerOne’s ability to navigate these early challenges. The company’s commitment to transparency, collaboration, and community-driven security has helped shape the modern bug bounty landscape.By embracing open communication and a community-driven approach, HackerOne has not only revolutionized the way companies approach bug bounty programs but has also inspired a new era of collaboration in the cybersecurity industry.
Revenue Streams and Growth Strategies of HackerOne
As the pioneer in the bug bounty space, HackerOne has evolved over the years to become a robust platform for organizations to engage with the global hacking community. One key aspect that fuels their growth is their diverse revenue streams, which include program fees, platform revenue, and consulting services.HackerOne generates significant revenue from program fees, where organizations pay for the privilege of hosting a bug bounty program on their platform.
Program fees account for a substantial portion of HackerOne’s revenue, as more organizations are now turning to bug bounties as a means to identify and mitigate vulnerabilities in their systems. For instance, in 2020, HackerOne announced that they had partnered with the US Department of Defense to launch a bug bounty program, with the US government paying a staggering $150,000 to bug bounty hunters.Platform revenue is another crucial component of HackerOne’s revenue streams.
The platform charges a fee for every valid vulnerability reported by researchers. The platform also earns revenue from its subscription-based model, where researchers pay a fee to access exclusive bug bounty programs. Moreover, HackerOne offers a feature called “HackerOne Score” which provides organizations with insights and analytics on their bug bounty performance, providing them with a competitive edge in the market place.HackerOne’s consulting services are also an essential revenue stream.
The company offers advisory services to organizations to help them set up and manage their bug bounty programs, including training programs for CISOs and security teams on how to effectively engage with the hacker community.
| Revenue Stream | Description | Percentage Contribution to Revenue (2020) |
|---|---|---|
| Program Fees | Revenue generated from program fees paid by organizations hosting bug bounty programs on HackerOne’s platform. | 60% |
| Platform Revenue | Revenue earned from fees charged per valid vulnerability reported by researchers, as well as subscription fees from researchers accessing exclusive bug bounty programs. | 25% |
| Consulting Services | Revenue generated from advisory services, including training programs for CISOs and security teams. | 15% |
Prioritization of Program Fees
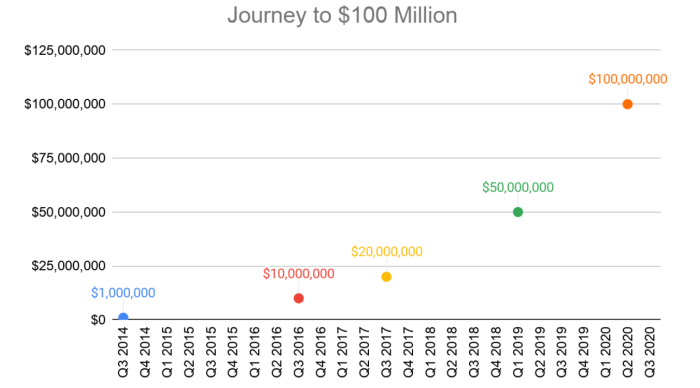
Program fees have become a critical component of HackerOne’s revenue streams, as more organizations are now willing to pay for the privilege of hosting bug bounty programs on their platform. By prioritizing program fees, HackerOne has created a robust ecosystem that encourages organizations to engage with the global hacking community.The revenue generated from program fees is substantial, with HackerOne’s platform handling over $100 million in bug bounties in 2020.
As more organizations are now willing to pay for the privilege of hosting bug bounty programs, HackerOne’s revenue from program fees is likely to continue growing.
Strategic Partnerships and Advisory Board
HackerOne’s strategic partnerships with organizations and enterprises have been instrumental in fueling the company’s growth. By partnering with industry leaders such as Uber, Twitter, and Microsoft, HackerOne has been able to expand its reach and influence within the bug bounty community.HackerOne’s advisory board, comprising industry experts and thought leaders, provides valuable guidance and insights that inform the company’s growth strategy.
The board’s expertise and network have been essential in shaping HackerOne’s vision and mission, ensuring that the company remains at the forefront of the bug bounty industry.
“At HackerOne, we believe that bug bounties are not just a compliance check – they are a critical component of an organization’s security posture.”
The advisory board’s influence has been evident in HackerOne’s growing presence in the bug bounty industry. With a network of over 700,000 active hackers and researchers, HackerOne has become the go-to platform for organizations seeking to identify and mitigate vulnerabilities in their systems.HackerOne’s growth has also been driven by its strategic partnerships with organizations and enterprises. By partnering with industry leaders, HackerOne has been able to expand its reach and influence within the bug bounty community, driving revenue growth and cementing its position as a leader in the industry.
Expansions and Acquisitions
In addition to prioritizing program fees, strategic partnerships, and consulting services, HackerOne has also been expanding its offerings through strategic acquisitions. In 2020, HackerOne acquired Synack, a vulnerability assessment platform that provides organizations with a comprehensive view of their security posture.The acquisition has expanded HackerOne’s offerings, enabling organizations to access a broader range of vulnerability assessment and penetration testing services.
Moreover, the acquisition has provided HackerOne with access to Synack’s vast network of researchers and hackers, further expanding the company’s reach within the bug bounty community.The expansion of HackerOne’s offerings through strategic acquisitions has been instrumental in driving revenue growth and reinforcing the company’s position as a leader in the bug bounty industry.
The Impact of HackerOne’s Bug Bounty Model on Cybersecurity
The bug bounty model developed by HackerOne has revolutionized the way organizations approach cybersecurity by promoting proactive vulnerability identification and disclosure. By incentivizing skilled hackers to identify and report security vulnerabilities, HackerOne’s model has significantly contributed to the improvement of cyber security. This innovative approach not only strengthens the security posture of organizations but also fosters a culture of collaboration between hackers, organizations, and cybersecurity experts.
Advantages of HackerOne’s Bug Bounty Model
The bug bounty model developed by HackerOne offers several advantages to organizations, including cost-effectiveness, increased security coverage, and accelerated vulnerability disclosure. The model allows organizations to:
Tap into a pool of skilled hackers who can identify security vulnerabilities that might have gone undetected by in-house security teams.
Eliminate the need to invest in expensive security testing tools and infrastructure.
Access a wider range of testing methodologies and techniques, including social engineering and penetration testing.
The bug bounty model also provides incentives for hackers to participate, including monetary rewards, recognition, and the opportunity to demonstrate their skills.
Disadvantages of HackerOne’s Bug Bounty Model
While the bug bounty model offers several advantages, it also has some disadvantages and potential risks. These include:
The risk of exploitation by malicious hackers who may use the bug bounty platform to gain unauthorized access to systems or steal sensitive information.
The potential for vulnerability exploitation without proper disclosure, resulting in unauthorized access to sensitive data or systems.
Compliance issues, as organizations may struggle to ensure that all identified vulnerabilities are properly disclosed and addressed.
To mitigate these risks, HackerOne has implemented various measures, including secure communication protocols, multi-factor authentication, and a thorough due diligence process for hackers.
Contribution to Cyber Security Improvement
HackerOne’s bug bounty model has made significant contributions to the improvement of cyber security through proactive vulnerability identification and disclosure. The model:
Allows organizations to identify and address vulnerabilities in a timely and cost-effective manner, reducing the risk of security breaches and data theft.
Fosters a culture of collaboration and transparency between hackers, organizations, and cybersecurity experts, promoting the sharing of knowledge and best practices.
Enables the development of more effective security testing methodologies and techniques, ultimately strengthening the security posture of organizations.
The impact of HackerOne’s bug bounty model on cyber security is undeniable, and its continued growth and adoption are expected to shape the future of cybersecurity for years to come.
Industry Adoption and Growth
The bug bounty model developed by HackerOne has been widely adopted by organizations across various industries, including finance, healthcare, and technology. The model’s growth is driven by the increasing recognition of its value in improving cyber security, as well as the need for organizations to demonstrate their commitment to security and transparency.As the demand for effective security solutions continues to grow, HackerOne’s bug bounty model is poised to play a leading role in shaping the future of cybersecurity, promoting collaboration, and driving innovation.
HackerOne’s bug bounty model has become an essential tool in the fight against cyber threats, and its impact is likely to be felt for years to come.
With its growing adoption and continued innovation, the bug bounty model is poised to play a leading role in shaping the future of cybersecurity.
HackerOne’s Expansion into New Markets

HackerOne’s expansion into new markets marks a significant milestone in the company’s journey to democratize the bug bounty landscape. With a vision to create a level playing field for hackers and organizations alike, HackerOne has been consistently pushing the boundaries of innovation and accessibility.As HackerOne ventured into international waters, the company recognized the importance of engaging with diverse hacker communities.
This involved developing localized programs, forging partnerships with local industry leaders, and adapting to regional regulations. By doing so, HackerOne successfully created a platform for hackers from various cultural backgrounds to participate in bug bounty programs, thereby fostering global collaboration and expertise sharing.
Evolving Partnerships and Localized Programs
The key to HackerOne’s successful expansion into new markets can be attributed to its strategic partnerships and localized programs. By leveraging the expertise of local partners, HackerOne was able to tailor its services to meet the unique needs of each region, thereby establishing a strong foothold in new markets.Local partners played a crucial role in facilitating HackerOne’s expansion, as they possessed an in-depth understanding of regional regulations, cultural nuances, and industry dynamics.
By partnering with local industry leaders, HackerOne was able to tap into a network of trusted experts, thereby ensuring the successful implementation of its bug bounty programs in new markets.In addition to partnerships, HackerOne also developed localized programs to cater to the specific needs of each region. These programs were designed to accommodate regional language preferences, cultural sensitivities, and industry-specific requirements.
By doing so, HackerOne was able to create a platform that was both inclusive and accessible, thereby empowering a diverse range of hackers to participate in bug bounty programs.Here are some of the key benefits of localized programs and partnerships:
-
Enhanced cultural sensitivity:
By partnering with local industry leaders and developing localized programs, HackerOne was able to tap into regional cultural nuances and create a platform that was both inclusive and accessible.
-
Increased regional expertise:
Local partners and regional experts brought valuable insights and expertise to the table, enabling HackerOne to tailor its services to meet the unique needs of each region.
-
Better regulatory compliance:
By partnering with local industry leaders and adapting to regional regulations, HackerOne ensured that its bug bounty programs were fully compliant with local laws and regulations.
Here’s an example of how local partnerships and localized programs helped HackerOne expand into new markets:
For instance, in Japan, HackerOne partnered with the likes of GMO Internet and Cybertrust to develop localized programs that catered to the unique needs of the Japanese market. By leveraging the expertise of local partners, HackerOne was able to create a platform that was both culturally sensitive and regionally relevant.
As HackerOne continues to push the boundaries of innovation and accessibility, its expansion into new markets serves as a testament to the power of strategic partnerships and localized programs. By fostering global collaboration and expertise sharing, HackerOne has created a platform that is truly democratizing the bug bounty landscape.
Ethical Hacking in the Modern Era: The Case of HackerOne

Ethical hacking has become a cornerstone of modern cybersecurity, and HackerOne has played a pivotal role in shaping this field. As the world becomes increasingly interconnected, the threat landscape is evolving at an alarming rate. Cyber threats can compromise sensitive information, disrupt critical infrastructure, and put lives at risk. In this context, ethical hacking has emerged as a vital tool for organizations to identify vulnerabilities and fortify their defenses.
The Importance of Ethical Hacking
Ethical hacking is the practice of simulating cyber attacks on a system, network, or application to identify weaknesses and vulnerabilities. It involves using authorized techniques to bypass security measures, often using similar tactics as malicious hackers. By employing ethical hacking, organizations can proactively identify vulnerabilities, prioritize remediation efforts, and strengthen their cybersecurity posture.
Challenges and Controversies in Ethical Hacking
Despite its importance, ethical hacking is not without its challenges. One of the primary concerns is the risk of unauthorized access to sensitive information. To mitigate this risk, organizations must ensure that their ethical hacking programs are well-defined, with clear guidelines and protocols in place. Another challenge is the difficulty in finding skilled and experienced ethical hackers. In response to these challenges, HackerOne has implemented various measures to promote and facilitate ethical hacking practices.
HackerOne’s Approach to Ethical Hacking
HackerOne’s platform has revolutionized the way organizations approach ethical hacking. By providing an inclusive and secure environment, HackerOne enables organizations to access a global community of skilled hackers. This community includes researchers, security experts, and hackers who contribute to the identification and remediation of vulnerabilities.
- Program Development and Management: HackerOne provides guidance and support to organizations in developing and managing their bug bounty programs, ensuring that the entire process, from planning and execution to communication and reward, is carried out effectively and efficiently.
- Community Engagement and Collaboration : HackerOne facilitates collaboration between hackers and organizations, fostering open communication and knowledge sharing. This helps in identifying vulnerabilities and prioritizing remediation efforts.
- Security Research and Development : HackerOne invests in research and development, focusing on improving the security posture of its platform and the tools used by hackers to identify vulnerabilities.
HackerOne’s model of incentivizing responsible disclosure and fostering collaboration between hackers and organizations has proven to be an effective strategy in addressing cybersecurity threats.
Addressing Concerns and Challenges
HackerOne has taken proactive measures to address the challenges and concerns surrounding ethical hacking. For instance, the company has implemented robust guidelines and protocols to ensure that hackers operate within the boundaries of the law. Additionally, HackerOne has established a Code of Conduct that Artikels the expectations and responsibilities of hackers participating in bug bounty programs.
Fostering a Culture of Responsible Disclosure
HackerOne promotes a culture of responsible disclosure, where hackers are encouraged to participate in identifying vulnerabilities while respecting the intellectual property and sensitive information of organizations. By fostering this culture, HackerOne has created a community of hackers and researchers who prioritize the security and integrity of the digital world.
The Intersection of Artificial Intelligence (AI) and Human Oversight in HackerOne’s Operations: Hackerone Net Worth
HackerOne, a pioneer in the bug bounty market, has been harnessing the power of Artificial Intelligence (AI) to revolutionize the way they identify and prioritize vulnerabilities. By leveraging AI tools, HackerOne aims to streamline their operations, freeing up human experts to focus on the most critical aspects of bug discovery.The AI-powered system, which includes advanced machine learning algorithms, has proven to be a game-changer in the world of bug bounty hunting.
By analyzing vast troves of data, AI can identify patterns and anomalies that might have gone unnoticed by human eyes. However, it’s essential to understand that AI is not a replacement for human experts, but rather a complementary tool that enhances their capabilities.
The Role of AI in Bug Identification
AI plays a crucial role in facilitating bug identification and prioritization by performing tasks such as:*
-
* Scanning large codebases to identify potential vulnerabilities
* Analyzing network traffic to detect suspicious patterns
* Using natural language processing to identify potential security threats
* Creating predictive models to forecast potential vulnerabilities
The AI system can process vast amounts of data in a fraction of the time it would take a human expert to do so, allowing HackerOne to identify and prioritize vulnerabilities more efficiently. This enables the company to focus on the most critical issues, ensuring that the most severe vulnerabilities are addressed first.However, it’s essential to note that AI has limitations, particularly when it comes to understanding the nuances of human behavior and contextual factors.
For instance, AI might struggle to identify social engineering attacks or zero-day exploits, which require a deep understanding of human psychology and the ability to think creatively.
The Limitations of AI in Bug Discovery
Despite its many advantages, AI has its limitations when it comes to bug discovery:*
-
* AI might struggle to identify vulnerabilities that require human intuition and creativity
* AI can be fooled by sophisticated attacks or manipulated data
* AI may not fully understand the context and implications of a vulnerability
– Human experts play a vital role in ensuring the accuracy and reliability of AI-generated findings, making them an essential part of HackerOne’s operations.
Human experts bring a level of nuance and understanding that AI cannot replicate, ensuring that AI-generated findings are thoroughly vetted and validated before they are presented to clients.
The Synergies between AI and Human Oversight
The relationship between AI and human oversight is one of symbiosis, where each complements the other’s strengths and weaknesses. By leveraging AI to identify and prioritize vulnerabilities, human experts can focus on the most critical issues, using their expertise to validate and improve AI-generated findings.
“The key to success is not to replace human experts with AI, but to augment their capabilities and create a synergistic relationship that unlocks new levels of efficiency and effectiveness.”
This synergy is the hallmark of HackerOne’s operations, where human experts and AI work together to create a unified and powerful approach to bug bounty hunting.
Popular Questions
Q: What is HackerOne’s revenue model?
HackerOne generates revenue through program fees, platform revenue, consulting services, and partnerships with organizations. The company’s partnerships with enterprises and advisory board contribute to its growth.
Q: How does HackerOne’s bug bounty model impact cybersecurity?
HackerOne’s model incentivizes hackers to identify vulnerabilities, leading to proactive vulnerability identification and disclosure. This model has significantly improved cybersecurity by empowering hackers to work with organizations to fix vulnerabilities.
Q: What sets HackerOne apart from its competitors in the bug bounty industry?
HackerOne’s robust platform, advisory board, and expert guidance set it apart from competitors. The company’s ability to leverage AI tools to facilitate bug identification and prioritize vulnerabilities for human assessment also gives it a competitive edge.
Q: Where is HackerOne expanding its presence?
HackerOne is expanding its presence globally, entering new markets and engaging with diverse hacker communities. The company is developing localized programs, partnering with local experts, and leveraging AI tools to facilitate bug identification and vulnerability prioritization.
Q: How does HackerOne contribute to digital transformation in organizations?
HackerOne’s platform assists organizations in digital transformation by identifying and addressing security risks in their digital products. The company’s expertise in cybersecurity and digital transformation drives proactive security practices, enabling organizations to stay ahead of emerging threats.